You didn’t want your web history to show, so you went ‘incognito’. You didn’t want your web activity to be monitored or recorded by your ISP, so you got a Virtual Private Network. But now you might have discovered that WebRTC bypasses your VPN and could leave you open to IP leaks. This article is here to tell you how to protect yourself against privacy leaks when you’re using a VPN, and for those of you who aren’t in the know, let’s start by clearing up what WebRTC and DNS are and why they can be a risk.
First, what is WebRTC?
Web real-time communication software or WebRTC is an element of some browsers and apps that aids things like video and audio playback – making them run more smoothly. Better Skype video and web calls, great. Before WebRTC came along, websites could only communicate in real-time through unreliable plugins.
However, while it helps to improve the functionality of Google Hangouts, Discord and other communication tools, WebRTC can also leave your online privacy at risk.
What are the risks?
For VPN users, privacy and anonymity are the name of the game. You use a virtual private network to add a layer of encryption to your data, and to hide your IP address so that you can browse without being tracked for targeted ads, or snooped on by other third parties. But what many VPN users aren’t aware of is that WebRTC can leak their IP address even when browsing via VPN.
Certain browsers ignore whether or not you have a VPN when transferring information using WebRTC, and will send domain name system (DNS) requests (including your IP address) outside of your VPN. This means that you think you’re browsing anonymously, but your own unique IP address is actually visible, putting your data at risk.
What’s the deal with DNS?
When you type the name of a website into your browser, your computer makes a series of requests using the domain name system, to translate the words you’ve typed into the numerical IP address associated with that site. As you browse the internet, the IP address you’re using to make those DNS queries is also logged.
Just as WebRTC can leak your IP address by sending requests outside of your VPN, DNS details can be leaked even with that extra protection in place. It usually happens because your VPN has been misconfigured, but also occurs if your internet service provider (ISP) has set up its service to force connected devices into using their own DNS servers to resolve queries. This means that instead of the DNS process happening via a VPN server, it goes through one that logs your IP.
Detecting a leak
It’s not always obvious if your computer is using its default settings and not routing data requests through your VPN’s servers. Use a WebRTC leak checker to see if you’re at risk using the following steps:
- Connect to your VPN
- Open the WebRTC Leak Checker
- If the IP address that appears is from your ISP, you have a leak
Google Chrome and Mozilla Firefox are both key culprits for causing WebRTC leaks because of their built-in real-time comms functions. If you’re concerned that a Chrome extension could also be causing a DNS leak, you can check it this way:
- Install VPN extension for your provider
- Connect to your VPN
- Type ‘chrome://net-internals/#dns’ into the browser
- Click Clear host cache
- Open a new tab and go to any website
- Check the DNS information in the previous tab.
Changing DNS Servers
If it turns out that your default DNS server is that of your ISP, you can always switch to another DNS server. An added bonus of this often includes faster internet speeds.
You could choose a server like Open DNS or Google Public DNS which shouldn’t override your VPN, but the simplest thing to do is to set your VPNs DNS server details as the default.
Once chosen, you will need to change your system settings. Windows 10 users:
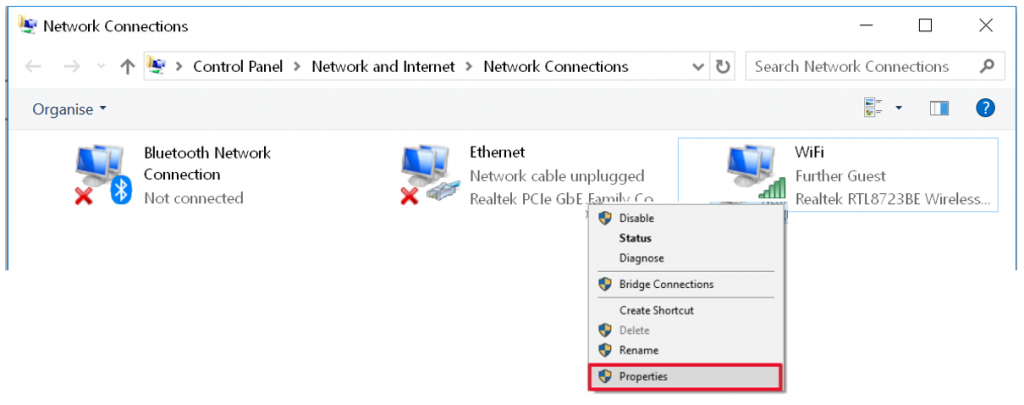
- Go into settings/control panel
- Click on Network and Internet
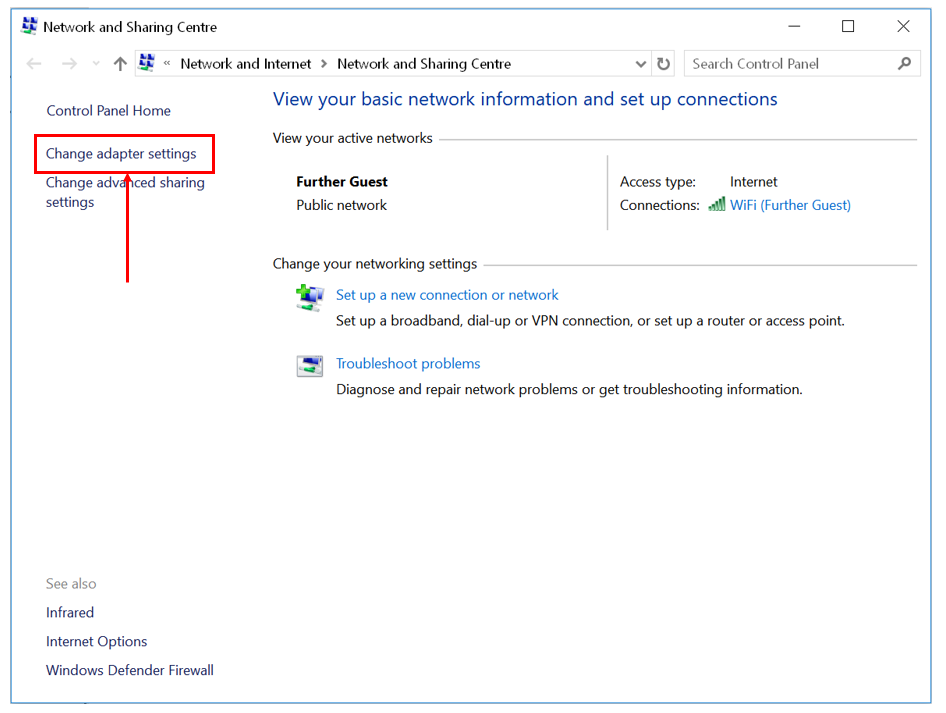
- Click on Network and Sharing Center
- On the left pane, click on Change adapter settings
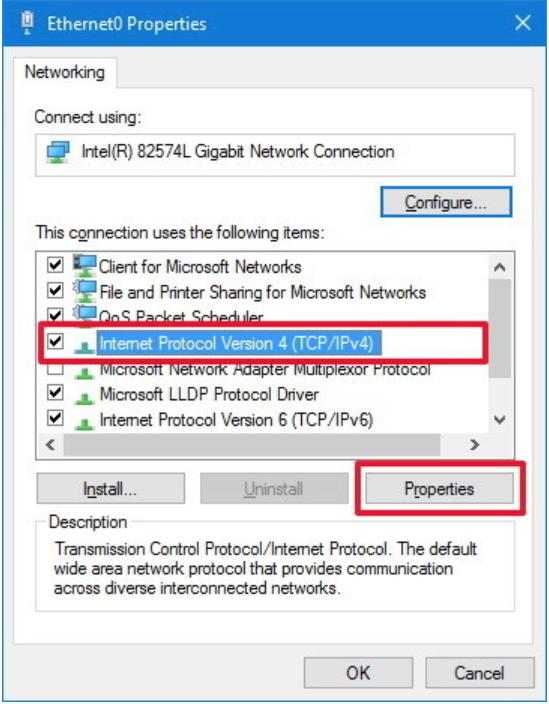
6. Select Internet Protocol Version 4 (TCP/IPv4) from the list
7. Click the Properties button
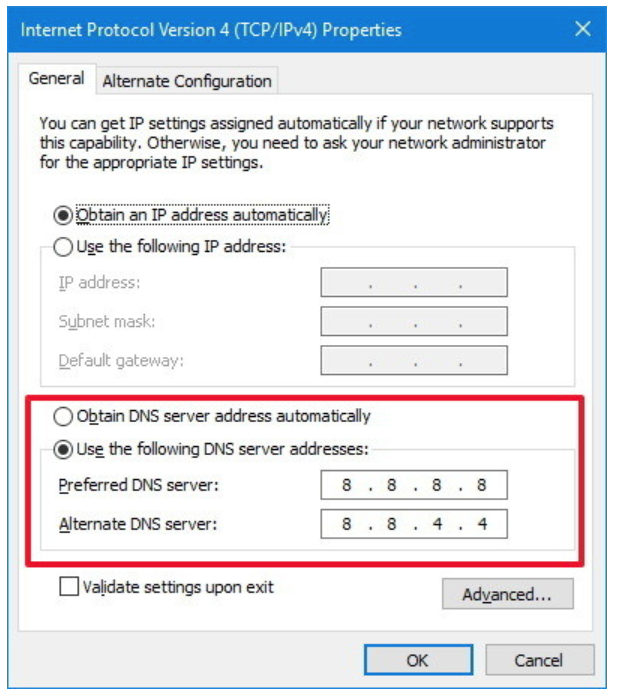
8. Click the Use the following DNS server addresses option
9. Type your preferred and alternate DNS server addresses
10. Enter the DNS servers you want to use (for example: Google Public DNS addresses: 8.8.8.8 and 8.8.4.4)
11. Click OK
12. Click Close to apply the new DNS settings. Your task is complete: you are now using the new DNS settings.
Android users can change their DNS server, but it only when using WiFi – not data. Find the appropriate settings when you hit the Menu button and choose Advanced while you’re in the WiFi setup screen.
How to prevent WebRTC leaks
If you use:
- Chrome
- Desktop
- Install the WebRTC Network Limiter extension. This official Google extension switches off WebRTC’s IP-leaking feature. Ensure you’re using the official Google extension or a reputable VPN as many fake extensions exist.
- Mobile
- In the mobile version of Chrome, paste chrome://flags/#disable-webrtc into the browser and change it to ‘disabled’.
- Firefox
- Navigate to about:config and search for the media.peerconnection.enabled setting. Once located, change it to ‘disabled’.
- Desktop
The best protection against WebRTC and DNS leaks
The best way to protect yourself is to ensure you’re using a good quality VPN that has built-in safeguards against WebRTC and DNS leaks. If your VPN is diverting traffic through their DNS servers instead of your ISP’s, then you’re protected.
Reputable VPN clients include a kill switch which can be a serious privacy saver in the event of a leak, cutting your internet connection the moment a drop in your VPN connection is detected. This prevents your data being transmitted without encryption, as well as keeping your IP safely hidden under cover.