Cybersecurity firm Fortinet said that cybercriminals are becoming smarter and faster in how they leverage exploits to their advantage. Citing its recent report, the company said that they are maximizing their efforts by targeting an expanding attack surface and by using iterative approaches to software development facilitating the evolution of their attack methodologies.
Fortinet said its analysis focused on critical and high-severity detections demonstrates an alarming trend with 96% of firms experiencing at least one severe exploit. Almost no firm is immune to the evolving attack trends of cybercriminals. In addition, nearly a quarter of companies saw cryptojacking malware, and only six malware variants spread to over 10% of all organizations.
“Cyber adversaries are relentless. Increasingly, they are automating their toolsets and creating variations of known exploits. Of late, they are also more precise in their targeting, relying less on blanket attempts to find exploitable victims. Urgently, organizations must pivot their security strategy to address these tactics. Organizations should leverage automated and integrated defenses to address the problems of speed and scale, utilize high-performance behavior-based detection, and rely on AI-informed threat intelligence insights to focus their efforts on patching vulnerabilities that matter,” said Rajesh Maurya, Regional Vice President, India & SAARC, Fortinet.
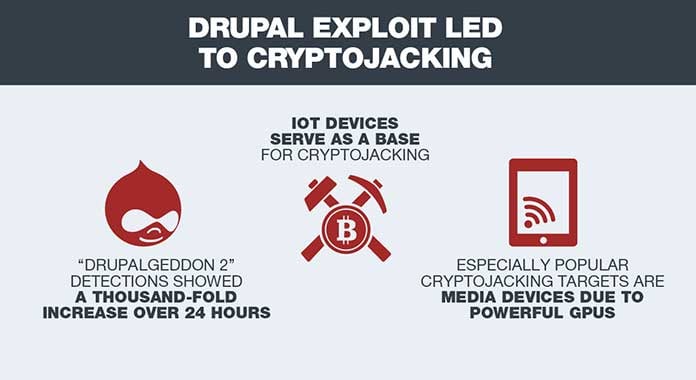
The report said mining for cryptocurrency continues, cybercriminals added IoT devices, including media devices in the home to their arsenals. They are an especially attractive target because of their rich source of computational horsepower, which can be used for malicious purposes. Attackers are taking advantage of them by loading malware that is continually mining because these devices are always on and connected. In addition, the interfaces for these devices are being exploited as modified web browsers, which expands the vulnerabilities and exploit vectors on them. Segmentation will be increasingly important for devices connected to enterprise networks as this trend continues.
According to the report, data on botnet trends gives a valuable post-compromise viewpoint of how cybercriminals are maximizing impact with multiple malicious actions. WICKED, a new Mirai botnet variant, added at least three exploits to its arsenal to target unpatched IoT devices. VPNFilter, the advanced nation-state-sponsored attack that targets SCADA/ICS environments by monitoring MODBUS SCADA protocols, emerged as a significant threat. It is particularly dangerous because it not only performs data exfiltration but can also render devices completely inoperable, either individually or as a group. The Anubis variant from the Bankbot family introduced several innovations. It is capable of performing ransomware, keylogger, RAT functions, SMS interception, lock screen, and call forwarding. Keeping tabs of morphing attacks with actionable threat intelligence is vital as creativity expands.
The report asserted that malware authors have long relied on polymorphism to evade detection. Recent attack trends show they are turning to agile development practices to make their malware even more difficult to detect and to counter the latest tactics of anti-malware products. GandCrab had many new releases this year, and its developers continue to update this malware at a rapid pace. While automation of malware attacks presents new challenges, so does agile development because of the skills and processes to roll out new evading releases of attack methods. To keep pace with the agile development cybercriminals are employing, organizations need advanced threat protection and detection capabilities that help them pinpoint these recycled vulnerabilities.
Adversaries are selective in determining what vulnerabilities they target. With exploits examined from the lens of prevalence and volume of related exploit detections, only 5.7% of known vulnerabilities were exploited in the wild. If the vast majority of vulnerabilities won’t be exploited, organizations should consider taking a much more proactive and strategic approach to vulnerability remediation.
When comparing application count usage across industries, the report said, government use of SaaS applications is 108% higher than the mean and is second to education in the total number of applications used daily, 22.5% and 69% higher than the mean, respectively. The likely cause for the higher usage in these two industry segments is a greater need for a wider diversity of applications. These organizations will require a security approach that breaks down silos between each of these applications, including their multi-cloud environments, for transparent visibility and security controls.
“In India JavaScript, cryptojacking websites and exploits targeting known vulnerabilities in enterprise web systems running Apache Struts (CVE-2017-5638), Oracle WebLogic Server (CVE-2017-10271, CVE-2017-3506) and older IIS 6.0 web servers (CVE-2017-7269) continue to be prevalent in Q2 2018. This was followed closely by exploits targeting vulnerabilities in D-Link devices. Risky software posing as driver packs, adware and malware leveraging on a known Microsoft Office exploit (CVE 2017-11882) was the most prevalent in this region, followed by JavaScript-based cryptojacking malware. Andromeda botnet continues to be prevalent, even though its infrastructure was already taken down in Q4 2017. As highlighted in our recent Q2 2018 Threat Landscape Report, of the 103,786 vulnerabilities published on the CVE List since it began, 5,898 (5.7%) were exploited in the wild. The 5.7% encompasses the popular exploits that were outlined above. Threat actors are constantly looking for easy targets with known vulnerabilities; the mistake of not addressing these vulnerabilities in a timely manner increases the risk of organizations getting compromised,” said Gavin Chow, Network and Security Strategist, Fortinet Asia Pacific.















